Spatial computing is not simply a new interface layer built on familiar infrastructure. It is a fundamentally new threat surface, one where authentication must operate across immersive 3D environments, ambient sensor arrays, mixed reality overlays, and decentralized protocol stacks simultaneously. The assumption that conventional password systems, standard TLS, or even legacy biometric scanners can scale into this paradigm is a critical miscalculation. Jett Optics is directly challenging that assumption, engineering optical encryption and gaze-based biometric authentication that are purpose-built for the cyber-physical realities of spatial computing, decentralized identity, and the emerging agentic web.
Table of Contents
- Understanding optical encryption and spatial computing security
- Jett Optics' privacy-preserving spatial encryption and authentication flow
- The mechanics of chained authentication using gaze biometrics
- Integration with existing authentication systems: OAuth, JWTs, and Solana
- Why independent validation and robust threat modeling are non-negotiable
- Take the next step with Jett Optics spatial encryption solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Optical encryption basics | Physical-layer encryption using light boosts security for spatial computing environments. |
| Biometrics and decentralized attestation | Using gaze biometrics and DePIN attestation provides more privacy-preserving authentication. |
| Chained authentication and entropy | Jett Optics' flow increases resilience by linking gaze patterns to blockchain proofs and measuring entropy. |
| Hybrid integration | JettAuth SDK combines traditional OAuth and blockchain protocols for robust authentication. |
| Validation and threat modeling | Investors and professionals must demand independent testing and rigorous threat models before adoption. |
Understanding optical encryption and spatial computing security
To appreciate why Jett Optics' approach is significant, it is essential to understand what optical encryption actually does, and why spatial computing makes traditional security architectures insufficient.
Optical encryption transmits and encodes information using coherent light, leveraging physical-layer mechanisms that introduce complexity no purely digital protocol can replicate. Physical-layer optical encryption is empirically grounded in measurable mechanisms, with security relying on noise and chaff engineering and mode matching at the signal level. This means the security model is not solely algorithmic. It is physically constrained, tying confidentiality to the properties of the transmission medium itself.
Spatial computing amplifies the stakes. Environments built around augmented and mixed reality merge digital layers directly with physical space, creating new categories of attack vector. Authentication can no longer rely purely on something a user knows or possesses. It must account for the user's physical orientation, environmental noise, ambient hardware signals, and the latency characteristics of real-time spatial rendering.
Relevant security considerations for spatial computing include:
- Sensor fusion attacks: Adversaries can correlate data from multiple ambient sensors (camera, LiDAR, inertial measurement units) to reconstruct sensitive behavioral patterns.
- Spatial replay attacks: Pre-recorded spatial sessions can be injected to spoof contextual authentication signals.
- Environmental noise interference: Radio frequency and optical interference in physical environments can corrupt signal integrity, creating exploitable authentication gaps.
- Man-in-the-middle risks at the cyber-physical boundary: Where digital overlays interact with physical infrastructure, interception points multiply.
"Security in spatial computing is not a software problem with a software solution. It is a systems-level challenge that demands physical-layer cryptographic modeling, biometric signal fidelity, and decentralized attestation to function at the required trust tier."
This is precisely the problem space where Jett Optics operates, building at the intersection of optical spatial encryption and human biometric signals to produce authentication architectures that spatial computing environments actually require.
Jett Optics' privacy-preserving spatial encryption and authentication flow
Jett Optics' most distinctive framework for spatial authentication is Phantom Mode, a protocol layer that binds gaze biometrics with Decentralized Physical Infrastructure Network (DePIN) attestation to deliver privacy-preserving authentication without exposing raw biometric data. Privacy-preserving spatial encryption for the agentic web ties gaze biometrics and DePIN attestation into a spatial encryption layer designed specifically for agentic web authentication workflows.
The design philosophy here is significant. Rather than centralizing biometric templates in a server-side database, Phantom Mode generates cryptographic commitments derived from gaze data, which are then attested through a decentralized network. The raw biometric signal never leaves the device perimeter in plaintext. This approach directly addresses gaze biometric compliance requirements under GDPR and equivalent frameworks, because no personally identifiable biometric template is stored in a form that can be retrieved, reversed, or breached.
Here is how Phantom Mode's authentication flow is structured:
- Gaze capture: The AGT (Agentive Gaze Tensor) engine captures high-resolution gaze vectors, fixation durations, and saccadic patterns from the user's optical environment.
- Tensor encoding: Raw gaze data is mapped into a weighted AGT representation, which functions as a spatial biometric signature rather than a simple fixation point.
- Spatial encryption layer: The AGT output is encrypted using the spatial encryption protocol, binding the biometric signal to the session context and environmental state.
- DePIN attestation: An attestation node within the DePIN network validates the encrypted biometric commitment without decrypting or accessing the underlying gaze data.
- Authentication assertion: The attested result is returned to the agentic web privacy encryption layer as a verified identity claim, completing the authentication event.
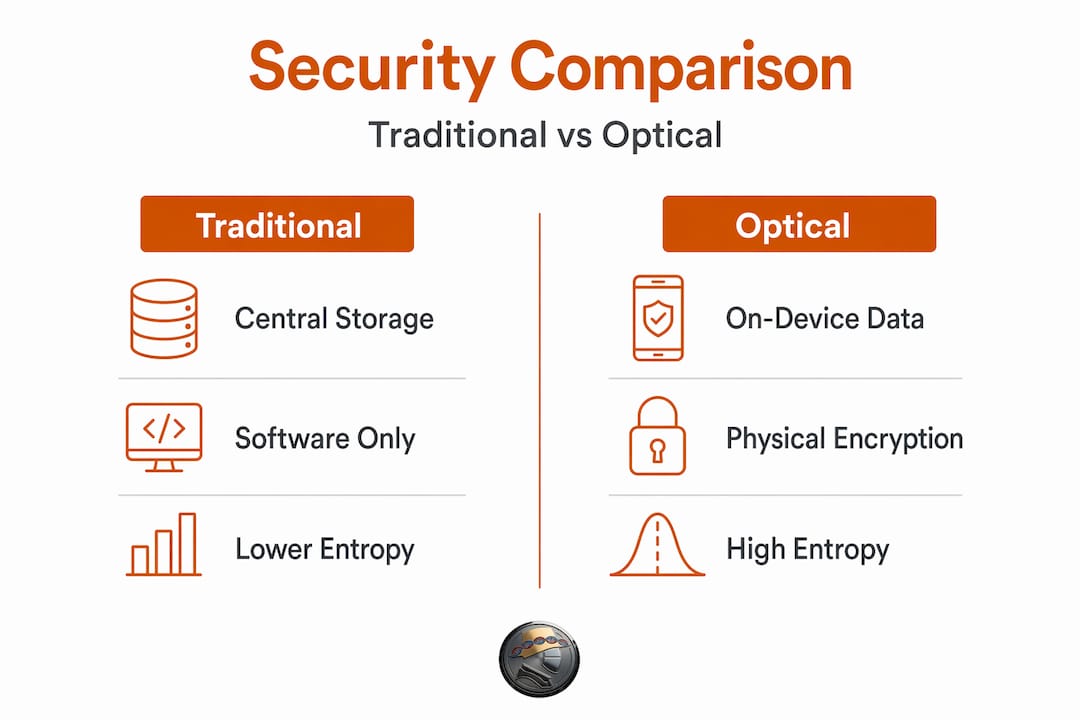
Comparison: Traditional vs. Jett Optics spatial authentication
| Dimension | Traditional biometric auth | Jett Optics Phantom Mode |
|---|---|---|
| Biometric storage | Centralized template database | On-device; no raw export |
| Attestation model | Server-side verification | DePIN decentralized attestation |
| Environmental awareness | None | Spatial context-bound |
| Replay attack resistance | Low to moderate | High (spatial + gaze entropy) |
| Compliance posture | Varies by implementation | Privacy-by-design architecture |
| Agentic web compatibility | Not designed for it | Native integration |
Pro Tip: When evaluating any spatial biometric authentication vendor, ask specifically whether the raw biometric template leaves the endpoint. If it does, the compliance surface area and breach risk expand dramatically, regardless of the encryption layer around it.
The mechanics of chained authentication using gaze biometrics
The authentication chain Jett Optics engineers around gaze biometrics is technically layered and worth examining in detail. At its core sits the AARON Router, a protocol architecture that maps gaze pattern data to biometric signatures, bridges these to on-chain proofs, and produces opaque attestations. The AARON Router authentication architecture uses a gaze pattern mapped to a biometric signature, with OPT𝕏 Bridge, opaque proof, and on-chain attestation, where entropy directly strengthens authentication resistance.
Entropy is the critical variable in this architecture. Shannon entropy, calculated over the distribution of AGT weight values, measures how unpredictable and varied the gaze pattern is during an authentication event. A user with a high-entropy gaze pattern produces a biometric signature that is computationally harder to approximate, replay, or synthesize. Low-entropy patterns, such as someone staring at a fixed point, produce weaker authentication signals, and the system can flag these for additional challenge steps.
The full authentication chain flows as follows:
- Gaze vector collection: Temporal sequences of gaze vectors are sampled at high frequency across the spatial field.
- AGT weight calculation: Vectors are weighted by fixation duration, saccadic velocity, and spatial region to produce the AGT tensor.
- Shannon entropy scoring: Entropy is calculated across the AGT weight distribution; scores below threshold trigger secondary authentication.
- OPT𝕏 Bridge encoding: The AGT output is encoded through the OPT𝕏 Bridge, which applies optical spatial encryption before the data moves off-device.
- On-chain attestation: The encrypted commitment traverses the blockchain attestation layer, producing an opaque proof that confirms identity without revealing the underlying biometric content.
Gaze entropy and authentication strength
| Entropy level | AGT weight distribution | Authentication strength | Recommended response |
|---|---|---|---|
| High (>2.5 bits) | Varied, spatially distributed | Very strong | Single-factor sufficient |
| Medium (1.5 to 2.5 bits) | Moderate variation | Adequate | Monitor or light 2FA |
| Low (<1.5 bits) | Concentrated, static | Weak | Trigger additional challenge |
This architecture does face real challenges that security teams and investors should model carefully. Sensor spoofing, where a fabricated visual input is fed to the gaze capture hardware, is a non-trivial attack vector. Replay attacks using recorded gaze sessions require robust session binding and temporal nonce injection to neutralize. Gaze drift introduced by fatigue or optical hardware calibration variance can degrade biometric fidelity. Threat modeling in authentication systems must account for each of these edge cases, especially in deployments where the physical environment is uncontrolled.
The spatial authentication flow Jett Optics has designed positions entropy scoring and DePIN attestation as layered defenses against precisely these attack classes, though real-world deployment testing across diverse hardware configurations remains the standard of proof.
Integration with existing authentication systems: OAuth, JWTs, and Solana
One of the practical questions for security teams evaluating spatial biometric authentication is how it integrates with existing protocol stacks. Jett Optics answers this through the JettAuth SDK, which is built to function as a hybrid authentication layer rather than a replacement for established standards. The JettAuth SDK combines OAuth 2.0 PKCE, Solana signMessage, and Ed25519 JWTs to produce a robust hybrid authentication architecture.
This integration strategy matters because no enterprise or decentralized application can afford to discard its existing identity infrastructure overnight. JettAuth is designed to slot into, and harden, what is already there:
- OAuth 2.0 PKCE flow: The Proof Key for Code Exchange extension is used to protect authorization code flows against interception, particularly critical in environments where ambient network signals can be captured. JettAuth preserves this standard and augments it with spatial biometric gating at the token issuance stage.
- Solana signMessage: Solana's cryptographic message signing layer provides decentralized attestation of identity, binding the authenticated session to a specific wallet keypair. This makes identity assertions verifiable on-chain without requiring trust in a central identity provider.
- Ed25519 JWT issuance: Rather than relying on older HMAC-SHA256 JWT signing schemes, JettAuth issues tokens signed with Ed25519, an elliptic curve signature algorithm that is both compact and computationally efficient, providing cryptographic integrity across the session lifecycle.
- Gaze biometric gating: Before any OAuth token or JWT is issued, the JettAuth SDK requires a valid gaze biometric assertion from the AGT engine, ensuring the person initiating the authentication event is physically present and matched.
- Session binding and expiry: Sessions are temporally bound and tied to the spatial context at authentication time, reducing the window of opportunity for session hijacking or token theft.
Pro Tip: Ed25519 is broadly considered a strong choice for high-assurance token signing because it resists a range of side-channel attacks that affect RSA and even some ECDSA implementations. If your JWT infrastructure still uses RS256, migrating to Ed25519-signed tokens as a baseline is worth prioritizing independently of any spatial biometric layer.
The hybrid authentication integration model that JettAuth implements means security teams can adopt spatial biometrics incrementally, testing gaze-gated flows in high-risk session contexts first, then expanding to broader coverage as hardware availability and compliance posture are confirmed. This is a realistic deployment pathway, not a theoretical migration blueprint.
Why independent validation and robust threat modeling are non-negotiable
Here is an opinion worth stating plainly: no amount of architectural sophistication replaces empirical, third-party validation of a security system. This is true for established protocols, and it is especially true for novel ones.
Jett Optics' technical artifacts are at the protocol and software level, and independent validation, threat model review, and edge-case evaluation are the appropriate standard for due diligence at this stage. That is not a critique of the architecture. It is the standard every serious security investment decision should require.
Gaze biometrics introduce edge cases that laboratory conditions do not always surface. Users with nystagmus, vestibular disorders, or prosthetic eye conditions will behave differently in gaze capture systems. High-brightness spatial environments, aggressive IR interference, and consumer-grade AR hardware with lower optical resolution than development prototypes all affect AGT signal fidelity. These are real conditions, not theoretical edge cases, and they belong in any comprehensive threat model.
Investors evaluating spatial encryption startups should ask three questions: What attack classes does your threat model formally enumerate? What is your process for sensor spoofing detection and countermeasure validation? Has any independent security research team reviewed your attestation architecture under adversarial conditions? If those questions produce vague answers, the diligence for spatial encryption threshold has not been met, regardless of how compelling the underlying protocol design is.
Jett Optics' architecture exhibits genuine technical depth. The combination of entropy-scored gaze biometrics, DePIN attestation, OPT𝕏 Bridge encryption, and Ed25519-anchored JWTs represents a coherent, multi-layer security model. That design quality makes the call for formal independent validation more urgent, not less. The stronger the security claim, the more rigorous the testing required to substantiate it. That is not skepticism. It is how serious security infrastructure gets built.
Take the next step with Jett Optics spatial encryption solutions
Security professionals and tech investors looking to engage with the most technically advanced spatial authentication architecture currently being developed have a clear entry point. Jett Optics is building the infrastructure that the next generation of secure spatial environments will depend on, from AGT-powered gaze biometrics to quantum-resistant optical encryption and DePIN-attested identity flows.
Whether you are architecting authentication for a mixed reality enterprise deployment, evaluating spatial encryption protocols for portfolio inclusion, or researching the frontier of biometric cryptography, Jett Optics offers the technical depth and protocol sophistication to meet that need. Explore spatial encryption solutions to review the full protocol documentation, SDK specifications, and attestation architecture. To understand the broader vision spanning optical security, decentralized identity, and spatial augments, learn more about Jett Optics and the platform's expanding ecosystem of security-first spatial technologies.
Frequently asked questions
How does Jett Optics' Phantom Mode enhance spatial computing security?
Phantom Mode integrates gaze biometrics with DePIN attestation to provide privacy-preserving spatial encryption for authentication on agentic web apps, ensuring raw biometric data never leaves the device perimeter in plaintext form.
What is the role of entropy in Jett Optics' authentication chain?
Entropy measures the variability of the gaze pattern through Shannon entropy of the AGT weights; higher entropy means stronger authentication resistance, while low-entropy sessions trigger additional challenge steps automatically.
How does JettAuth SDK integrate traditional and blockchain-based authentication?
JettAuth SDK combines OAuth 2.0 PKCE, Solana signMessage, and Ed25519 JWTs for unified hybrid authentication, enabling spatial biometric gating to layer directly on top of established authorization protocol flows.
Why should investors request independent validation for optical encryption startups?
Independent validation ensures that security claims, particularly for protocol-level innovations, are tested against real-world edge cases, adversarial sensor conditions, and diverse hardware environments before any deployment commitment is made.