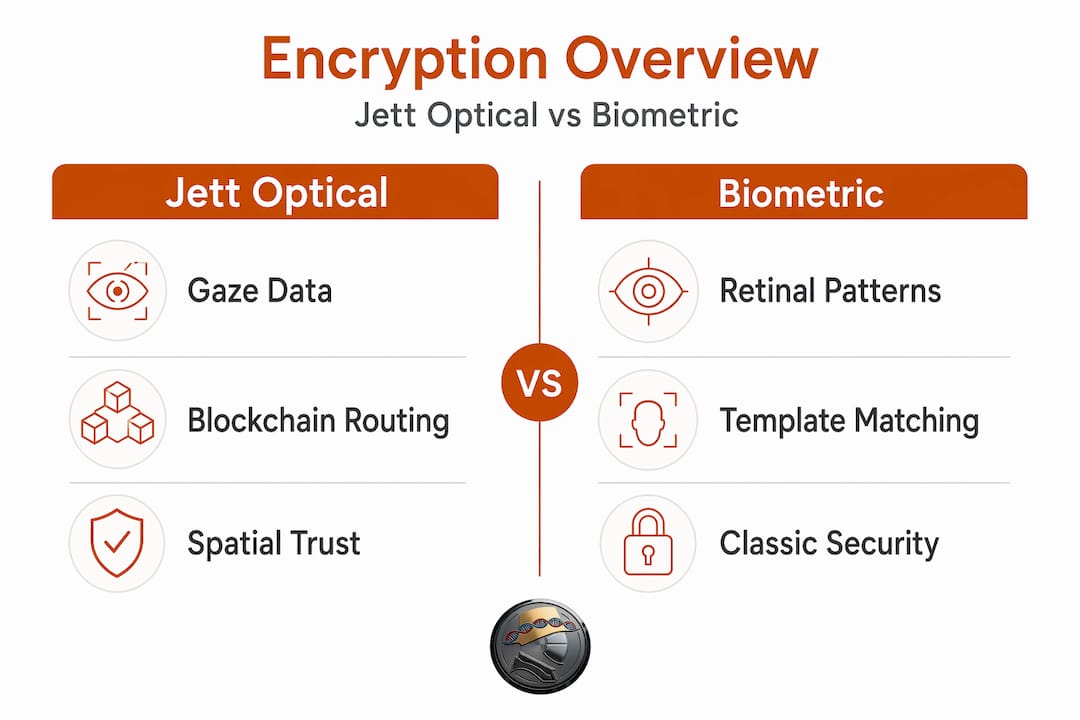
Traditional software encryption was engineered for a flat, session-based digital world. It was never designed to authenticate where you are, what you're looking at, or whether your intent is genuine in three-dimensional space. As spatial computing platforms mature and biometric modalities move from convenience features to primary trust anchors, the gap between conventional cryptographic stacks and what modern deployments actually require is widening fast. Jett Optics addresses that gap directly with the OPTX ecosystem, a gaze-anchored, blockchain-routed, privacy-preserving trust architecture built for the agentic web. This article unpacks the technical infrastructure, examines the peer-reviewed science behind optical and biometric encryption, and gives cybersecurity leaders a rigorous framework for evaluating deployment readiness.
Table of Contents
- Why spatial computing demands a new trust architecture
- Inside the Jett Optical Encryption trust stack
- Optical and biometric encryption: What the science actually shows
- Practical guidance: Executive due diligence for spatial encryption
- The uncomfortable truth about optical encryption claims
- Explore Jett Optics solutions for verified spatial trust
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Spatial trust challenge | Spatial computing security needs new authentication and privacy models beyond software-only encryption. |
| Jett ecosystem approach | Jett Optical Encryption combines gaze biometrics, blockchain proofs, and SDK tooling for layered trust. |
| Evidence versus claims | Jett’s workflows are documented and analogous to peer-reviewed literature, but specific optical encryption mechanics remain unproven publicly. |
| Due diligence is critical | Executives and CISOs should require verifiable public benchmarks and validate deployments against real threat models. |
| Future-proofing security | Active participation in industry challenge programs and open validation will set spatial security leaders apart. |
Why spatial computing demands a new trust architecture
The integration of physical and digital environments in spatial computing fundamentally breaks the assumptions that underpin classical public-key infrastructure. PKI verifies identity at the credential layer. It does not verify presence, attention, or intent within a volumetric session. When a user interacts with a mixed-reality interface, the trust surface expands from a device endpoint to a continuous, three-dimensional interaction stream. That shift requires authentication primitives that can operate on spatial signals, not just static credentials.
Gaze, specifically the temporal and directional properties of where a user looks, is one of the highest-entropy biometric signals available in spatial environments. It is continuous, difficult to spoof without physical access, and encodes behavioral patterns that are statistically unique across individuals. However, the same properties that make gaze valuable also make it sensitive. Capturing and routing gaze data without privacy-preserving controls creates a surveillance vector, not a security one.
The spatial encryption overview at Jett Optics frames this challenge precisely: the goal is not simply to encrypt gaze data in transit but to use the gaze signal itself as a cryptographic primitive, generating proofs that authenticate without exposing raw biometric streams. That architectural distinction matters enormously for compliance and for adversarial robustness.
The broader optical encryption research community is pursuing similar ambitions at the physical layer. A Nature Communications study demonstrates spatiotemporal noise chaffing optical encryption achieving transmission rates exceeding the terabit-per-second scale. That result confirms the theoretical ceiling for optical channel security is extremely high. However, peer-reviewed literature also makes clear that production validation of specific mechanisms remains rare. "Optical encryption" as a category spans structured light encoding, orbital angular momentum multiplexing, metasurface-based phase encoding, and noise chaffing. Each has distinct threat models, implementation requirements, and performance envelopes. Executives evaluating any optical encryption product should treat the category label as a starting point, not a guarantee.
Key requirements for spatial trust architectures include:
- Intent verification: Authentication must confirm that the user is actively engaging, not just present at an endpoint.
- Continuous session integrity: Trust cannot be asserted once at login; it must be maintained across the spatial session.
- Privacy-preserving proof generation: Biometric signals must produce cryptographic proofs without exposing raw data to intermediaries.
- On-chain auditability: For regulated environments, attestations must be verifiable and tamper-evident.
- Interoperability with modern infrastructure security protocols: Spatial trust layers cannot exist as isolated silos; they must integrate with existing enterprise security stacks.
"Optical encryption" is a catch-all term. Before trusting any product narrative, verify both the theoretical layer being invoked and the specific production benchmarks available for that implementation.
With the stakes set, let's decode what makes the Jett infrastructure different under the hood.
Inside the Jett Optical Encryption trust stack
The OPTX ecosystem is designed as a system-level trust architecture, not a feature bolted onto an existing authentication flow. Its core innovation is the use of gaze-derived biometric signals as the root of a cryptographic trust chain that routes through on-chain attestation infrastructure. Understanding the trust flow requires tracing each component from signal capture to final attestation.

The AARON router code documents the core pipeline: JETT Auth captures a biometric signature derived from gaze, which is then routed through the OPTX Bridge and AARON to generate an Opaque Proof. That proof connects to x402 payments and attestations settled on Solana Mainnet. The architecture separates the biometric capture layer from the proof generation layer, which is a critical privacy design choice. Raw gaze data does not traverse the routing infrastructure. Only the derived cryptographic artifact does.
The numbered trust flow operates as follows:
- Gaze capture: The JETT Auth module captures Agentive Gaze Tensor (AGT) data from the user's spatial session, encoding directional, temporal, and fixation properties.
- Biometric signature generation: The AGT data is processed into a biometric signature, a high-entropy representation that is mathematically derived from the gaze pattern but is not reversible to raw gaze coordinates.
- Opaque Proof routing: The biometric signature is submitted to the OPTX Bridge, which applies zero-knowledge-style proof construction to generate an Opaque Proof without exposing the underlying signature to the routing layer.
- AARON arbitration: The AARON router arbitrates between proof validity, session context, and payment/attestation requirements, enforcing policy at the routing layer.
- On-chain attestation: Valid proofs are attested on Solana Mainnet, creating an immutable, auditable record of session authorization without storing biometric data on-chain.
| Trust flow stage | Input | Output | Cryptographic control |
|---|---|---|---|
| JETT Auth | Raw gaze stream (AGT) | Biometric signature | Entropy extraction, one-way derivation |
| OPTX Bridge | Biometric signature | Opaque Proof | Zero-knowledge-style proof construction |
| AARON Router | Opaque Proof + session context | Routing decision | Policy enforcement, proof validation |
| Solana Mainnet | Routing decision | On-chain attestation | Immutable ledger, x402 payment settlement |
The jettoptx/joe-docs repository serves as the official documentation engine for the OPTX ecosystem, and pull requests within the repository reference JettChat dual-mode authentication in the README. Dual-mode auth is a significant usability and flexibility feature: it allows sessions to authenticate via gaze-based biometrics when spatial hardware is available, while falling back to conventional credential flows when it is not. That flexibility is essential for enterprise deployments where spatial hardware penetration is still partial.
The Jett Optics platform integrates blockchain and spatial security into a coherent reference architecture, supporting SDK-level integration for development teams building on the OPTX stack.
Pro Tip: When evaluating the OPTX integration, do not limit your audit to user-facing authentication flows. Specifically review the session creation endpoints and gaze proof generation interfaces for auditable artifacts. The security posture of the system depends on the integrity of the proof construction step, not just the final attestation record.
Now, how does Jett's approach compare with what's actually validated in peer-reviewed optical and biometric encryption research?
Optical and biometric encryption: What the science actually shows
The peer-reviewed literature on optical and biometric encryption provides important context for evaluating any product in this space. Published results are frequently impressive under controlled conditions, but the gap between laboratory benchmarks and production deployments is significant and often understated in product narratives.
On the biometric encryption side, a Scientific Reports framework demonstrates a multidimensional retinal biometric encryption system that generates three independent cryptographic keys from a single retinal vessel map. The cryptanalytic evaluation covers entropy analysis, randomness testing, collision resistance, and noise sensitivity. The threat model, however, is explicitly scoped to brute-force key guessing. Advanced attack vectors such as quantum cryptanalysis, side-channel exploitation, or adaptive chosen-plaintext attacks are outside the evaluated scope. That scoping is not a criticism of the research; it is a standard practice in academic cryptography to define threat model boundaries clearly. The implication for practitioners is that biometric encryption frameworks, including gaze-based ones, require separate evaluation against the specific threat models relevant to your deployment environment.
On the optical encryption side, the performance benchmarks in published literature are striking. Terabit-per-second transmission rates, high compression ratios, and strong autocorrelation resistance have all been demonstrated in controlled optical channel experiments. A Nature Communications physics study reinforces the point that these benchmarks are paper-specific and do not automatically transfer to product claims. The experimental setups, channel conditions, signal-to-noise regimes, and parameter sets that produce those results are tightly controlled. Replicating them in a production environment with variable hardware, ambient interference, and adversarial conditions is a materially different engineering problem.
Threat models commonly addressed in published biometric and optical encryption research include:
- Brute-force key guessing: Well-covered by high-entropy biometric key generation frameworks.
- Known-plaintext attacks: Addressed in several optical encryption schemes through noise chaffing and phase randomization.
- Physical-layer eavesdropping: Partially addressed by structured light and OAM-based schemes with channel-specific encoding.
- Replay attacks on biometric proofs: Addressed architecturally in systems that use session-bound, time-limited proof artifacts.
- Quantum cryptanalysis: Rarely addressed in current biometric encryption literature; requires explicit post-quantum design choices.
- Side-channel exploitation: Largely unaddressed in published optical biometric frameworks; an open research area.
For executive due diligence, treat any "optical encryption" claim as requiring independent verification. Demand public experimental setups, explicit parameter sets including channel conditions and SNR regimes, a clearly scoped threat model, and repeatable benchmarks before accepting performance claims at face value.
The detailed post-quantum security analysis available through Jett Optics addresses the quantum resistance dimension directly, which is a meaningful differentiator given how few biometric encryption frameworks explicitly design for post-quantum threat models.
With a clear sense of what's proven and what's plausible, how should decision-makers approach deploying trust infrastructure built on these emerging techniques?
Practical guidance: Executive due diligence for spatial encryption
Deploying spatial encryption infrastructure requires a structured evaluation process that goes beyond reviewing marketing documentation. The following framework applies to Jett's OPTX ecosystem and to any comparable spatial or biometric trust infrastructure under consideration.
- Audit the code repositories directly. The AARON router and documentation repositories are publicly accessible. Review proof construction logic, session binding mechanisms, and key derivation implementations before trusting the system with production workloads.
- Map the threat model explicitly. Identify which attack vectors are in scope for your deployment environment. Brute-force resistance is table stakes. Evaluate specifically for replay attacks, side-channel exposure, and quantum resilience if your threat horizon extends beyond five years.
- Demand reproducible session proof benchmarks. Session proof reproducibility, specifically whether the same gaze pattern under similar conditions generates consistent, valid proofs, is a core reliability metric. Request benchmark data or run controlled trials with your own test fixtures.
- Verify on-chain auditability end-to-end. Solana-based attestations are publicly verifiable. Confirm that the attestation records produced by AARON contain sufficient metadata to reconstruct session authorization decisions for compliance audits without exposing biometric data.
- Conduct integration audits at the SDK boundary. The SDK integration layer is where most enterprise security vulnerabilities originate. Engage a robust engineering evaluation partner to review SDK call patterns, error handling, and session lifecycle management.
- Participate in open challenge programs. If Jett or any comparable vendor offers adversarial challenge programs or third-party audit engagements, participate or require participation as a condition of deployment. Open challenge results are the strongest available signal of real-world robustness.
The reference architecture with blockchain security at Jett Optics provides a starting point for integration planning, but internal security teams should treat it as a blueprint requiring environment-specific adaptation, not a turnkey deployment specification.
Pro Tip: Never conflate the software SDK flow with true optical or physical layer resilience. The OPTX ecosystem's proof routing is a software architecture built on top of biometric signal capture. Its security properties are determined by the cryptographic integrity of the proof construction, not by the physical properties of the optical channel. Evaluate them separately.
With this mindset, let's challenge what the industry typically misses about spatial trust layers.
The uncomfortable truth about optical encryption claims
The industry has a pattern worth naming directly: vendors in emerging security categories frequently describe their mechanisms using the vocabulary of peer-reviewed research without providing the reproducible, adversarially tested evidence that peer review actually demands. "Optical encryption," "quantum-resistant biometrics," and "spatial trust" are all legitimate research domains. They are also phrases that can be applied to software architectures that have never been subjected to serious adversarial evaluation.
This is not an accusation directed at any specific vendor. It is a structural observation about how fast-moving security categories develop. The research validates the concept. The product ships the implementation. The gap between those two things is where real security risk lives, and it is rarely discussed openly in sales cycles.
The hard-won lesson from observing multiple cryptographic technology cycles is this: the strength of a security system is not determined by how sophisticated its protocol sounds. It is determined by whether real adversaries, independent researchers, and the broader security community can probe its edge cases and find them sound. Jett Optics' public repositories and documentation are a meaningful step toward that transparency. The next step, for Jett and for the category, is open challenge programs, published audit reports, and protocol specifications detailed enough for independent cryptanalysts to evaluate.
Those who commit early to transparent validation, including publishing parameter sets, threat model boundaries, and adversarial test results, will define what trustworthy next-gen spatial encryption actually means for the decade ahead. That is not a soft recommendation. It is the only path to institutional adoption at scale.
Explore Jett Optics solutions for verified spatial trust
Cybersecurity leaders evaluating spatial trust infrastructure need more than architectural diagrams. They need deployable reference models, auditable code, and integration pathways that fit within existing enterprise security frameworks.
Jett Optics provides exactly that through the OPTX ecosystem: a gaze-anchored, blockchain-routed, privacy-preserving trust stack with publicly accessible SDK documentation and on-chain attestation infrastructure. Whether you are piloting spatial authentication for a mixed-reality enterprise environment or evaluating biometric trust anchors for decentralized identity systems, the optical spatial encryption solutions at Jett Optics offer a technically grounded starting point. Explore the full reference architecture to assess integration requirements and begin your evaluation process with the depth the category demands.
Frequently asked questions
What is unique about Jett Optical Encryption compared to traditional encryption?
Jett leverages gaze-based biometric authentication and on-chain proofs, moving trust anchors into spatial and physical layers beyond classic software methods. The AARON router confirms that JETT Auth uses a biometric signature from gaze, routed through OPTX Bridge to Opaque Proof and x402 attestations on Solana Mainnet.
Are Jett's optical encryption techniques peer-reviewed?
No peer-reviewed publications directly validate Jett's specific mechanism, but the methods draw on concepts well-established in scientific optical encryption literature. Independent peer-reviewed research supports multiple optical dimension approaches without validating any specific product implementation.
What threat models are covered in biometric encryption research?
Published biometric encryption frameworks typically focus on brute-force key guessing, with limited coverage of quantum or advanced side-channel attacks. The Scientific Reports biometric encryption study explicitly scopes its cryptanalytic evaluation to brute-force threat models.
What due diligence steps should execs take before deploying optical encryption?
Demand reproducible benchmarks, integrate with open challenge programs, and always verify public evidence of adversarial robustness. Peer-reviewed optical encryption work consistently demonstrates that transparent verification of experimental setups and parameter sets is the baseline standard for credible claims.
Is Jett's gaze-based authentication compatible with existing security frameworks?
Jett supports dual-mode authentication, allowing flexible integration alongside common enterprise identity standards. The joe-docs repository references JettChat dual-mode auth, confirming that the OPTX ecosystem accommodates deployments where spatial hardware availability is partial or transitional.