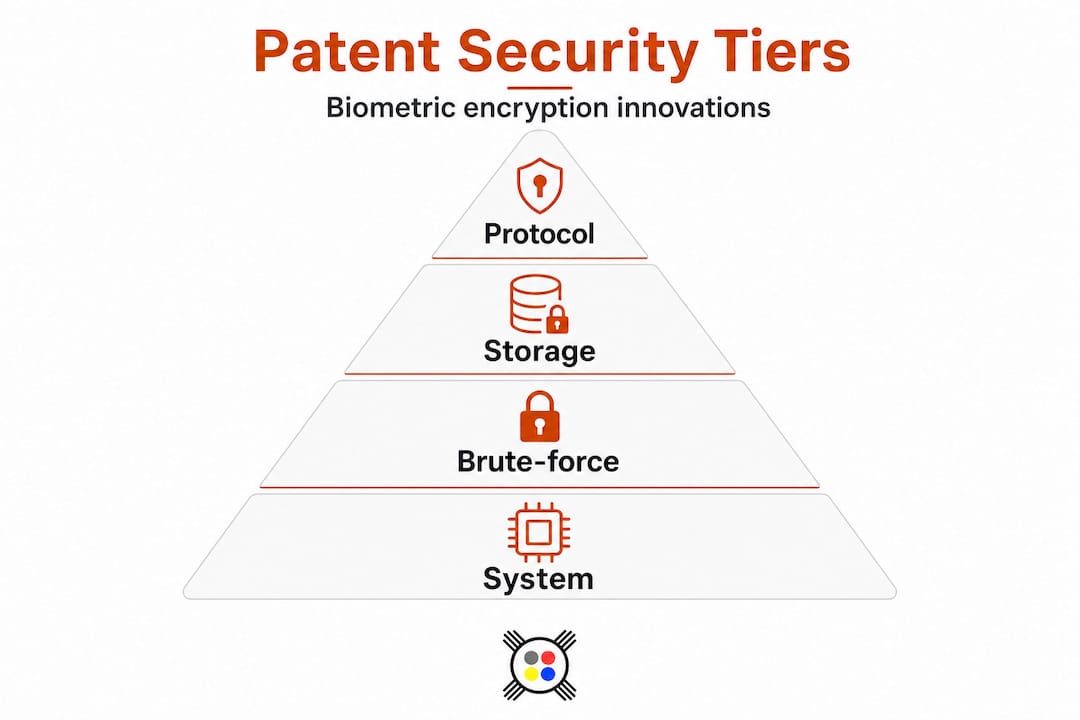
Biometric encryption is advancing rapidly across enterprise, cloud, and decentralized authentication platforms, yet most practitioners still deploy systems that carry underestimated cryptanalytic exposure. Despite surging patent filings, a significant portion of production implementations remain vulnerable to offline brute-force attacks and cloud breach scenarios that existing patent claims fail to address at the system level. The patent landscape for privacy-preserving biometric authentication is evolving in three concurrent directions: protocol innovation (homomorphic encryption, secure multi-party computation), storage architecture reform (sharding, user-held keys, blockchain anchoring), and brute-force resistance engineering. Understanding precisely where each trend sits, what it actually protects, and where it leaves gaps is essential for any team architecting next-generation secure authentication platforms.
Table of Contents
- Understanding biometric encryption: Key approaches and patent motivations
- Privacy-preserving biometric authentication: Protocol innovation and application trends
- Securing biometric storage: Patented strategies for cloud and blockchain
- Brute-force resistance and real-world security: Addressing patent limitations
- What most miss in the biometric encryption patent race
- Harnessing innovation: Next steps with Jett Optics
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Patent activity surging | Biometric encryption patent filings now target privacy, storage innovation, and brute-force resistance. |
| Protocols must defend against real attacks | Low-entropy biometrics and cloud breaches require solutions beyond basic encryption. |
| Storage decentralization leads patent trends | Sharded, user-keyed, and blockchain-ready designs are increasingly patented for enhanced security. |
| Not all patents solve practical security | Effective protection demands real-world testing and critical evaluation of patent claims. |
Understanding biometric encryption: Key approaches and patent motivations
Biometric encryption, as a field, is not monolithic. It spans a range of constructions, each with distinct security assumptions, patent motivations, and real-world tradeoffs. The three dominant paradigms are fuzzy vault schemes, cancellable biometrics, and encrypted domain matching systems.
Fuzzy vault and key-binding constructions remain the most widely patented category. In a fuzzy vault, a cryptographic key is encoded within a polynomial structure, and the biometric measurement is used to reconstruct that polynomial during authentication. The system tolerates measurement noise inherent to biometric capture, whether fingerprint ridge displacement, iris dilation variance, or gaze trajectory deviation. As the MDPI survey confirms, biometric cryptosystems rely on key-binding and key-generation constructions such as fuzzy vaults to bind a cryptographic key to noisy biometric measurements. Patent filings in this category focus on improving the polynomial degree selection, error-correction code parameters, and chaff point generation to resist record multiplicity attacks.
Cancellable biometrics introduce a revocable transformation layer. Rather than storing raw biometric templates, the system applies a user-specific, non-invertible transformation before storage. If a template is compromised, the transformation parameters are updated, effectively "cancelling" the old credential. Patents in this space target specific transformation functions that preserve matching accuracy while providing unlinkability across databases.
Encrypted domain matching systems perform the comparison operation entirely within an encrypted space, never exposing the plaintext biometric template to the server. This is where optical spatial encryption approaches become particularly relevant, as spatial frequency representations of biometric signals can be matched in the encrypted domain without reconstruction.
The core motivations driving patent filings in all three categories are consistent:
- Handling noisy biometric measurements without degrading cryptographic key integrity
- Enabling secure key generation or reconstruction without exposing the biometric itself
- Supporting revocability and unlinkability across multiple enrollment instances
- Achieving provable security under standard cryptographic assumptions
"The challenge is not encrypting biometric data. The challenge is reconstructing a cryptographic key from measurements that are never identical twice, without leaking the underlying biometric in the process."
With that context established, we can now examine how privacy-preserving architectures and multi-party setups are shaping the patent landscape.
Privacy-preserving biometric authentication: Protocol innovation and application trends
The most significant patent activity in the last 24 months has concentrated on privacy-preserving authentication protocols, specifically those leveraging Homomorphic Encryption (HE) and Secure Multi-Party Computation (MPC). These approaches address a fundamental architectural problem: in traditional biometric authentication, the server must either receive the raw biometric or a decrypted template to perform matching, creating a single point of exposure.
HE allows the server to perform matching computations directly on encrypted biometric features, producing an encrypted result that only the authorized party can decrypt. MPC distributes the matching computation across multiple servers such that no single server ever holds a complete biometric representation or sufficient information to reconstruct one. As the ScienceDirect review documents, privacy-preserving protocols are organized by system scenario (client-server versus multi-server) and motivated by the need to prevent leakage of biometric features, often using HE and MPC.
The application scenarios where these protocols appear in patent filings are expanding:
- Banking and financial services login: HE-based matching enables a bank's authentication server to verify a fingerprint or iris match without the plaintext biometric ever leaving the client device.
- Cloud identity platforms: Multi-server MPC architectures distribute the matching burden across geographically separated nodes, eliminating single-server breach risk.
- DeFi and Web3 onboarding: Biometric-gated wallet access using zero-knowledge proofs derived from biometric measurements, enabling on-chain verification without storing the biometric on-chain.
- DePIN network authentication: Decentralized physical infrastructure networks require ambient, hands-free authentication, where gaze-based biometrics processed through MPC nodes offer a viable path.
| Protocol | Computation model | Storage model | Leakage risk | Scalability |
|---|---|---|---|---|
| Standard template matching | Plaintext server-side | Centralized | High | High |
| Fuzzy vault (key-binding) | Client-side reconstruction | Hashed template | Medium | Medium |
| Homomorphic encryption | Encrypted server-side | Encrypted template | Low | Low to medium |
| Secure MPC | Distributed computation | Sharded | Very low | Medium |
| ZK-proof biometric | Proof generation client-side | None (proof only) | Minimal | Improving |
Pro Tip: When evaluating HE-based biometric systems, verify that the noise parameters of the HE scheme are compatible with the expected biometric matching distance. Schemes optimized for integer arithmetic may introduce unacceptable false rejection rates when applied to continuous biometric feature vectors such as gaze trajectories or facial geometry embeddings.
Building on these protocol-centric innovations, the architecture and storage of biometric data itself have taken center stage in recent patents.
Securing biometric storage: Patented strategies for cloud and blockchain
Biometric data storage represents the highest-risk component in any authentication architecture. A compromised biometric template cannot be rotated like a password. Once a raw fingerprint or iris template is exposed, the credential is permanently degraded across every system where that biometric is enrolled. This irreversibility is precisely why patent filings have shifted aggressively toward distributed and user-controlled storage architectures.

The centralized cloud storage model, where a single server holds encrypted biometric templates, remains the most common deployment pattern and the most frequently breached. The attack surface includes not only the encrypted templates themselves but also the key management infrastructure, the matching service, and the audit logs. A breach at any layer can yield sufficient information for offline reconstruction attacks.
Recent patent activity addresses this through three primary architectural strategies:
- Data sharding: The biometric template is split into multiple mathematically independent shards, each stored on a separate server. As Dallas Innovates reports, patent architectures that split biometric data into shards distribute storage so that no single server holds the complete identifier, fundamentally changing the breach economics.
- User-held decryption keys: The encrypted template is stored server-side, but the decryption key never leaves the user's device. Matching occurs through a challenge-response protocol that requires the user's key to produce a verifiable authentication signal without decrypting the full template on the server.
- Double encryption for blockchain storage: Patent applications now cover encrypted-biometric template storage systems that use user-held keys and can optionally apply a second encryption layer to support storage on public blockchains, where data permanence and public readability create unique exposure vectors.
| Storage model | Breach impact | Key control | Revocability | Blockchain compatible |
|---|---|---|---|---|
| Single-server centralized | Total exposure | Server-held | Limited | No |
| Sharded multi-server | Partial, requires collusion | Server-held | Medium | Partial |
| User-held key | Template exposed, key safe | User-held | High | Partial |
| Double-encrypted blockchain | Minimal without user key | User-held | High | Yes |
Pro Tip: For organizations integrating biometric authentication with Web3 identity systems, double encryption with user-held keys is not optional. On-chain data is permanent and publicly readable. Any biometric-linked data stored on a public ledger without a user-controlled encryption layer is a regulatory and security liability, regardless of how the outer encryption is structured.
The deployment challenges for sharded and blockchain-anchored storage are real. Shard synchronization introduces latency that can degrade user experience in high-frequency authentication scenarios. Blockchain write costs for template updates must be factored into operational budgets. And user-held key architectures require robust key recovery mechanisms, because a lost key in a user-held system means permanent loss of authentication access.
Despite these advances, some edge-case vulnerabilities, especially brute-force attacks due to low biometric entropy, remain underestimated even in patented systems.
Brute-force resistance and real-world security: Addressing patent limitations
The entropy gap between biometric data and cryptographic passwords is one of the most consequential and least discussed vulnerabilities in deployed biometric encryption systems. A strong password, generated with a cryptographically secure random number generator, carries 128 or more bits of entropy. A fingerprint minutiae set, an iris code, or a gaze trajectory tensor carries significantly less, often in the range of 20 to 44 bits of effective entropy after accounting for measurement variability and the finite population of distinguishable biometric patterns.
This entropy gap creates a concrete attack surface. An adversary who obtains an encrypted biometric template or a fuzzy vault can mount an offline brute-force attack, systematically generating synthetic biometric samples and testing them against the stored construction. The IACR ePrint documents this explicitly: biometric encryption systems face a cryptanalytic edge case where biometrics can be low-entropy compared to passwords, enabling brute-force attacks if protocols are not designed for resistance, and proposes a dedicated brute-force resistant biometric protocol with studied performance characteristics.
"Encrypting a low-entropy biometric with a high-security cipher does not make the biometric high-entropy. It makes the cipher irrelevant. The attacker simply enumerates the biometric space."
Patent workarounds for this problem include several approaches worth examining carefully:
- Credential mixing: Combining the biometric measurement with a high-entropy secret (PIN, hardware token output) before key reconstruction, effectively raising the joint entropy of the authentication input.
- Double encryption with server-side rate limiting: Applying a second encryption layer whose key is server-controlled, forcing online interaction for each authentication attempt and enabling rate limiting and anomaly detection.
- Biometric-specific key stretching: Adapting password-hashing constructions (Argon2, scrypt) to the biometric domain, introducing memory-hard computation that raises the cost of each brute-force iteration.
To evaluate whether a patented or proposed biometric protocol actually provides brute-force resistance, implementers should work through the following assessment:
- Determine the effective entropy of the biometric feature vector in the target population, accounting for within-class variability and between-class separability.
- Identify whether the protocol requires online server interaction for each authentication attempt, or whether the stored artifact can be attacked offline.
- Verify that any key-binding construction uses an error-correction code whose parameters do not inadvertently reduce the search space for the cryptographic key.
- Confirm that credential mixing or key stretching is applied before the biometric is used as a cryptographic input, not after.
- Test the protocol against synthetic biometric generators, not just against standard biometric datasets, to assess resistance to generative adversarial attacks on the enrollment template.
Having mapped out the technical and patent-driven approaches, it is critical to reflect on lessons this landscape actually teaches organizations and developers.
What most miss in the biometric encryption patent race
The prevailing assumption among security teams evaluating biometric encryption patents is that a patent filing represents a validated, deployable solution. It does not. A patent demonstrates novelty and non-obviousness relative to prior art. It does not demonstrate provable security under a formal cryptographic model, resistance to all relevant attack classes, or fitness for any specific deployment environment.
The most significant gap in current patent filings is the system-level view. Individual patents address isolated problems: a better fuzzy vault construction, a more efficient HE matching protocol, a novel sharding scheme. What they rarely address is how these components interact when assembled into a production system, and where the seams between components create new attack surfaces. An HE-based matching protocol that is secure in isolation may become vulnerable when combined with a logging infrastructure that records encrypted query patterns, enabling traffic analysis attacks that reconstruct matching behavior over time.
Research advances like provable cloud security and brute-force resistance protocols from IACR ePrint publications are what actually change the security equation. These are not patents. They are peer-reviewed cryptographic constructions with formal security proofs under defined adversarial models. Implementers who treat patent filings as their primary technical reference are systematically missing the stronger, more rigorous work happening in the academic cryptography community.
The practical recommendation is to treat advanced spatial encryption approaches and peer-reviewed protocol designs as the baseline for technical evaluation, using patent filings as a secondary signal for understanding where commercial investment is concentrating. Patents indicate market direction. Research papers indicate security reality. The gap between the two is where most production vulnerabilities originate.
Organizations should also build continuous review into their biometric encryption architecture governance. The threat model for biometric data is not static. Advances in generative models, synthetic biometric generation, and quantum computing each shift the attack surface in ways that current patent claims do not anticipate. Architectural robustness, not compliance with the latest patent trend, is the durable security objective.
Harnessing innovation: Next steps with Jett Optics
The patent trends analyzed here, from privacy-preserving MPC protocols to double-encrypted blockchain storage and brute-force resistant key reconstruction, map directly onto the architectural challenges that forward-looking organizations are actively solving.
Jett Optics develops authentication systems that operate at the intersection of these trends, applying spatial encryption solutions to biometric inputs including gaze-derived AGT tensors, with quantum-resistant encryption layers and native compatibility with Web3 and DePIN network architectures. The platform addresses the entropy gap through credential mixing with optical spatial keys, and supports distributed biometric storage models that align with the sharded and user-held key architectures now emerging in leading patent filings. Security professionals and organizations evaluating next-generation biometric authentication platforms can explore the full technical scope of these capabilities through the Jett Optics platform, where spatial cryptography and biometric security converge into deployable, auditable systems.
Frequently asked questions
What types of biometric encryption patent strategies are most common?
The primary strategies are fuzzy vault and key-binding constructions, privacy-preserving protocols using HE and MPC, and advanced storage models including sharded data distribution and user-held decryption keys. As the MDPI survey confirms, biometric cryptosystems rely on these key-binding and key-generation constructions as their foundational security mechanism.
Why is brute-force resistance important in patented biometric systems?
Biometric feature vectors carry significantly lower entropy than cryptographic passwords, making offline enumeration attacks feasible against systems that do not implement specific resistance measures. The IACR ePrint establishes that low-entropy biometrics create an explicit cryptanalytic edge case that standard encryption alone cannot resolve.
How do patents address biometric storage in the cloud or on blockchains?
Recent filings use data sharding across multiple servers, user-held decryption keys that never leave the client device, and double encryption layers specifically designed for public blockchain storage scenarios. Patent applications now cover encrypted template storage systems that support optional double encryption to accommodate public ledger environments.
Are cloud-based biometric systems more vulnerable to attacks?
Yes. Centralized cloud storage concentrates breach risk at a single point, and most implementations lack the sharding or user-key architectures needed to limit exposure. Recent IACR research demonstrates scalable biometric authentication that targets provable security against cloud database breach, signaling that the academic community considers this a primary unresolved threat vector.