Organizations selecting biometric authentication platforms face a compounding risk: the technology that appears dominant today may carry exploitable weaknesses that attackers are already working to circumvent. Picking the wrong vendor or modality is not simply a procurement mistake—it can expose critical infrastructure to credential compromise, regulatory penalties, and reputational damage that take years to recover from. This guide gives cybersecurity executives a structured methodology for evaluating the true defensibility of biometric solutions, moving well beyond vendor marketing to assess R&D depth, anti-spoofing resilience, post-quantum readiness, and the capacity for rapid adaptation as the threat landscape shifts.
Table of Contents
- Understanding the biometric tech landscape
- Defining your competitive moat criteria
- Step-by-step biometric moat assessment framework
- Verifying and revisiting your moat over time
- The inconvenient truth: Moats don't last—here's what really works
- Explore next-gen bimodal defense with Jett Optics
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Market leaders focus | Top biometric firms succeed by investing in R&D and flexible multimodal systems. |
| Moat criteria matter | Strong security comes from features like anti-spoofing, adaptability, and privacy safeguards. |
| Continuous reassessment | Periodic reviews ensure that biometric defenses remain robust against new attack techniques. |
| Hybrid strategies win | Layering biometrics with other security methods is more sustainable than relying on any single solution. |
Understanding the biometric tech landscape
The biometric authentication market is not a monolith. It is a rapidly stratifying competitive field where a handful of established players hold significant advantages in IP, data assets, and enterprise integration, while emerging vendors challenge them with specialized modalities and novel cryptographic architectures.
Market leaders include NEC, Thales, IDEMIA, and Suprema, with growth CAGR projections of 14 to 19 percent driven primarily by BFSI and healthcare sector adoption. Their competitive strategies center on aggressive R&D investment and multimodal system development. These organizations have built defensible positions through large proprietary datasets, hardware integration, and regulatory compliance frameworks that take years for challengers to replicate.
The dominant modalities in enterprise deployments remain fingerprint, face recognition, and iris scanning, but their relative standing is shifting. Face recognition ratings have improved significantly in expert assessments, while fingerprint modalities have declined in perceived security due to documented spoofing vulnerabilities and dataset uncertainty. Iris and vein-pattern recognition are gaining ground in high-security contexts where liveness detection and anti-spoofing precision are non-negotiable.
Market leaders, modalities, and security track record
| Vendor | Primary Modalities | Notable Security Focus | Recent Track Record |
|---|---|---|---|
| NEC | Face, fingerprint, iris | Multimodal fusion, AI accuracy | Strong in law enforcement, airports |
| Thales | Face, fingerprint | Government ID, PKI integration | Regulatory compliance leadership |
| IDEMIA | Face, fingerprint, iris | Liveness detection, anti-spoofing | Large-scale banking deployments |
| Suprema | Fingerprint, face | Edge processing, on-device AI | Physical access control specialization |
Key factors currently reshaping the competitive landscape include:
- Regulatory pressure: GDPR, CCPA, and sector-specific mandates are forcing vendors to prioritize on-device processing and data minimization, which changes the architecture of competitive moats.
- AI-driven spoofing: Generative adversarial networks (GANs) and deepfake technologies are systematically degrading the reliability of face and fingerprint modalities that lack robust liveness detection.
- Quantum computing risk horizon: Post-quantum cryptographic standards are now being finalized by NIST, and biometric systems that rely on classical encryption for template storage face a medium-term obsolescence risk.
- Decentralized identity frameworks: Web3 and DePIN (Decentralized Physical Infrastructure Networks) architectures are creating demand for biometric systems that can operate without centralized template repositories.
Executives who understand these dynamics can move beyond evaluating vendors on accuracy benchmarks alone and begin assessing the structural depth of their competitive positioning. Integrating optical spatial encryption into authentication stacks represents one of the more forward-looking responses to these converging pressures.
Defining your competitive moat criteria
A competitive moat in biometric technology is not simply a high accuracy rate or a well-designed user interface. It is the combination of structural, technical, and organizational attributes that make a solution genuinely difficult for competitors or attackers to replicate or circumvent over a meaningful time horizon.
The most durable moats in this space are built on several interconnected pillars. First, proprietary data assets: vendors with access to large, diverse, and continuously updated biometric datasets can train models that generalize across demographic groups and environmental conditions far more reliably than those working from smaller or synthetic corpora. Second, multimodal fusion architectures: the ability to combine signals from multiple biometric modalities in real time, weighting them dynamically based on environmental context and confidence scores, creates a system resilience that single-modality solutions cannot match. Third, IP and algorithmic differentiation: patents on specific liveness detection methods, anti-spoofing layers, or template encryption schemes create legal and technical barriers to direct replication.

Biometric security presents a fundamental tension: enhanced user experience and security on one side, and the irreversible nature of biometric credentials on the other. Unlike passwords, a compromised biometric template cannot be reset. This asymmetry should weigh heavily in your moat evaluation criteria.
Criteria for evaluating moat strength:
- Anti-spoofing depth: Does the system use passive liveness detection, active challenge-response, or hardware-level depth sensing? Can it detect presentation attacks using printed photos, 3D masks, or synthetic video?
- Template revocability mechanisms: Does the vendor support cancelable biometrics or biometric salting to enable template invalidation without re-enrollment?
- Privacy-centric architecture: Is template processing performed on-device or at the edge, minimizing exposure of raw biometric data to centralized servers?
- Upgradability and patch responsiveness: How quickly has the vendor historically responded to newly published attack vectors? What is the update cadence for anti-spoofing models?
- Regulatory compliance posture: Does the solution support GDPR Article 9 requirements, CCPA sensitive data provisions, and sector-specific mandates such as HIPAA for healthcare deployments?
- Post-quantum readiness: Are biometric templates encrypted using quantum-resistant algorithms, or does the system rely on RSA or ECC schemes that are vulnerable to Shor's algorithm attacks?
"Zero-trust architecture and hybrid multi-factor systems that incorporate on-device biometric processing represent the most defensible posture against both spoofing attacks and the non-revocability risk inherent in biometric credentials." The organizations that treat biometrics as one layer in a layered security stack, rather than a standalone authentication mechanism, consistently demonstrate stronger long-term security outcomes.
Pro Tip: Do not overrate user experience metrics when evaluating biometric moats. Frictionless enrollment and fast match speeds are valuable, but they must never come at the cost of revocability controls or anti-spoofing rigor. The cost of a compromised, non-revocable biometric credential far exceeds the cost of a slightly more deliberate authentication flow. Pair post-quantum security requirements into your vendor RFP from the outset.
Step-by-step biometric moat assessment framework
A rigorous moat assessment requires a structured, repeatable process that goes beyond vendor-supplied benchmark data and analyst quadrant placements. The following framework is designed for security teams that need evidence-based evaluations they can defend to boards, regulators, and audit committees.
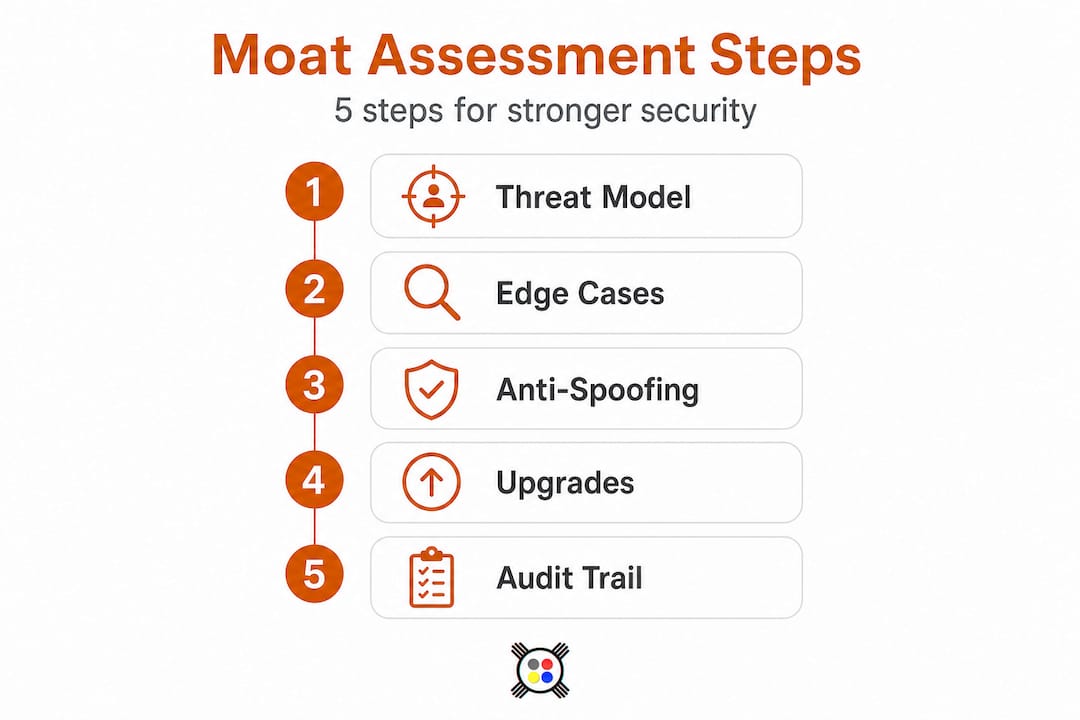
Step 1: Establish a baseline threat model. Before evaluating any vendor, document the specific threat actors, attack vectors, and regulatory environments relevant to your organization. A financial institution facing nation-state adversaries has fundamentally different requirements than a healthcare provider managing insider threat risks. Your baseline should include current and projected attack sophistication levels.
Step 2: Evaluate edge-case resilience. Edge cases in biometric systems include poor lighting conditions, demographic bias across age and ethnicity groups, temporal changes such as aging or injury, and identical twin scenarios. Effective mitigations require infrared and depth sensing hardware, multi-session template updating protocols, and expert-tuned decision thresholds. Require vendors to provide documented performance data across these specific scenarios, not just aggregate accuracy statistics.
Step 3: Conduct structured anti-spoofing stress tests. Using real-world threat models rather than laboratory benchmarks, test each candidate system against presentation attacks appropriate to your threat profile. This includes printed photo attacks, replay video attacks, 3D-printed mask attacks, and, for high-security deployments, adversarial AI-generated synthetic biometric inputs.
Step 4: Assess system upgradability and patch architecture. Request the vendor's documented history of security updates in response to published vulnerabilities. Evaluate whether anti-spoofing models can be updated independently of the core authentication engine, and whether updates can be deployed without requiring full re-enrollment of existing users.
Step 5: Review compliance and audit trail capabilities. Verify that the system generates immutable audit logs compatible with your regulatory reporting requirements. Assess whether the vendor's data processing agreements align with applicable privacy law, and whether the system architecture supports data residency requirements for cross-border deployments.
Comparison: Risk mitigation approaches by assessment dimension
| Assessment Dimension | Weak Moat Indicators | Strong Moat Indicators |
|---|---|---|
| Anti-spoofing | Single-layer, software-only detection | Hardware depth sensing plus AI liveness |
| Template security | Centralized storage, classical encryption | On-device processing, post-quantum encryption |
| Upgradability | Monolithic updates requiring re-enrollment | Modular model updates, backward compatible |
| Bias handling | Aggregate accuracy only | Demographic-stratified performance data |
| Compliance | Self-attested compliance claims | Third-party audit certifications |
Multimodal biometric fusion consistently outperforms single-modality systems across these dimensions, particularly in edge-case resilience and anti-spoofing depth, because it requires an attacker to simultaneously defeat multiple independent detection mechanisms.
Pro Tip: Simulate attacks using real-world threat models sourced from current threat intelligence feeds, not just the standardized attack scenarios in ISO/IEC 30107-3. Attackers do not constrain themselves to published test methodologies, and your assessment process should reflect that asymmetry.
Verifying and revisiting your moat over time
A competitive moat assessment is not a point-in-time certification. The biometric threat landscape evolves continuously, driven by advances in generative AI, new academic research on attack methodologies, and regulatory changes that can alter the legal defensibility of specific architectural choices.
Expert assessments of biometric modalities shift over time as new vulnerabilities are documented and new mitigations are validated. The decline in fingerprint modality ratings relative to face recognition illustrates how quickly a previously dominant technology can lose its security standing in expert consensus. Organizations that locked in fingerprint-only deployments five years ago without a reassessment process are now managing a degraded security posture they did not anticipate.
Red flags that your current moat is eroding:
- New exploit publications: Academic papers or CVE disclosures targeting your deployed modality or vendor's specific algorithm.
- Regulatory shifts: New guidance from data protection authorities that requires architectural changes, such as mandatory on-device processing or prohibition of centralized biometric databases.
- Vendor roadmap stagnation: Multi-quarter periods without meaningful security updates or anti-spoofing model improvements from your incumbent vendor.
- Demographic performance drift: Internal monitoring reveals declining match accuracy or increasing false rejection rates for specific user populations, indicating model degradation.
- Competitive capability leaps: Challenger vendors demonstrating materially superior anti-spoofing or post-quantum capabilities that your current vendor cannot match within a credible timeframe.
Monitoring should integrate vendor roadmap reviews on a quarterly cadence, continuous threat intelligence feeds focused on biometric attack research, and annual third-party penetration testing of your deployed authentication stack.
"Security is not a state you achieve—it is a process you sustain. Every biometric system that was considered unbreakable at deployment has eventually faced a credible attack vector. The organizations that maintain their security posture are those that treat reassessment as a core operational function, not an occasional audit exercise."
Structured reassessment intervals should be tied to your organization's risk tolerance and the sensitivity of the assets being protected. High-value targets warrant semi-annual full assessments; standard enterprise deployments should conduct comprehensive reviews annually, with continuous monitoring in between.
The inconvenient truth: Moats don't last—here's what really works
Here is the reality that vendor briefings will not surface: every competitive moat in biometric authentication is temporary. The cryptographic assumptions underlying today's strongest systems will be challenged by quantum computing advances. The anti-spoofing models that currently detect synthetic faces with high confidence are being systematically defeated by the next generation of generative models. Regulatory frameworks that currently permit centralized biometric processing are tightening in jurisdictions that represent significant portions of enterprise user bases.
The organizations that have maintained strong security postures over multi-year horizons share a common characteristic: they did not bet on a single technology being permanently superior. They built organizational processes for rapid validation and technology rotation. They implemented layered security architectures where biometrics function as one authentication factor among several, so that the compromise of any single layer does not constitute a system-level failure.
The most instructive examples come from financial services organizations that adopted fingerprint-based authentication in the early 2010s. Those that treated it as a permanent solution faced costly re-architecture projects when spoofing vulnerabilities became commercially exploitable. Those that had designed their authentication stacks with modality-agnostic middleware were able to layer in face recognition and liveness detection without disrupting existing user enrollment data.
True competitive advantage in biometric security is organizational as much as it is technological. It requires security teams with the expertise to evaluate emerging modalities before they become mainstream, vendor relationships that provide early access to roadmap developments, and architecture patterns that allow rapid integration of new authentication layers. Spatial encryption and gaze-based authentication represent exactly the kind of emerging layer that forward-looking organizations are evaluating now, before they become table stakes.
Pro Tip: Pair your biometric authentication layer with emergent technologies like future-proofing with spatial encryption to create a defense-in-depth posture that does not depend on any single modality remaining undefeated. The goal is not to find the perfect biometric technology—it is to build a system where the failure of any single component does not compromise the whole.
Explore next-gen bimodal defense with Jett Optics
Organizations that have worked through this assessment framework understand that the next frontier in authentication is not a better fingerprint sensor or a more accurate face recognition model. It is the integration of fundamentally different cryptographic primitives into the authentication stack.
Jett Optics builds exactly this kind of next-generation layer. The platform's approach to Jett Optics spatial encryption leverages Agentive Gaze Tensors (AGT) and quantum-resistant cryptographic protocols to create authentication mechanisms that are ambient, hands-free, and architecturally incompatible with the spoofing attack vectors that threaten conventional biometric modalities. For organizations building DePIN-ready identity infrastructure or securing high-value decentralized environments, Jett Optics provides the technical depth and roadmap alignment that the current generation of biometric vendors cannot offer. If your moat assessment has surfaced gaps in post-quantum readiness or anti-spoofing resilience, this is the technology layer worth evaluating next.
Frequently asked questions
What defines a competitive moat in biometric technology?
A competitive moat is the set of unique, hard-to-replicate features—such as advanced anti-spoofing, proprietary multimodal data assets, or rapid adaptability—that allow a solution to stay ahead of attackers and competitors. Market leaders focus competitive strategies on R&D investment and multimodal system development as the primary moat-building mechanisms.
How should organizations evaluate biometric vendors?
Assess vendors based on resilience to documented and emerging threats, multimodal support, template revocability, privacy architecture, and evidence of ongoing R&D investment. Vendors differentiate via R&D depth, multimodal fusion capabilities, and demonstrated security investment rather than accuracy benchmarks alone.
What are the main risks of current biometric modalities?
Risks include presentation spoofing attacks, demographic bias in model performance, privacy erosion from centralized template storage, and the fundamental inability to reset compromised biometric credentials. Fingerprint modality ratings have declined in expert assessments specifically due to documented spoofing vulnerabilities and dataset reliability concerns.
Do competitive advantages in biometrics last?
No competitive edge in biometric authentication is permanent; continuous validation, threat monitoring, and layered security architecture are essential as both attack sophistication and technology capabilities advance. Zero-trust and hybrid approaches are recommended precisely because static moats erode as attackers and regulators adapt over time.
